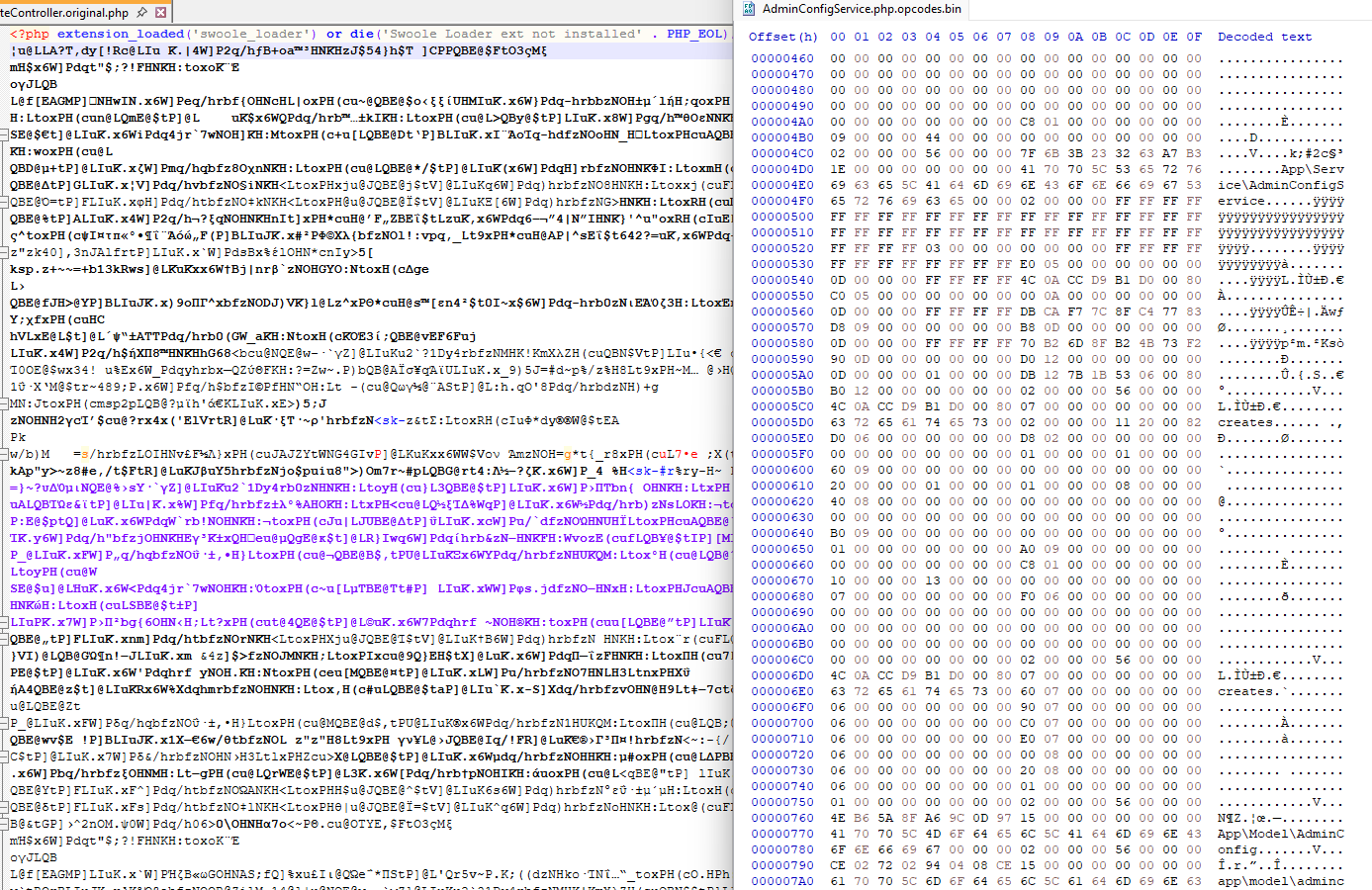
Swoole Compiler does far more than simple source-code obfuscation or encryption. Similar to solutions such as ionCube and SourceGuardian, it transforms PHP source code into low-level binary instructions that are executed through a dedicated runtime loader. Once compiled, the original human-readable PHP code is no longer directly accessible and can only be interpreted by a compatible version of the Swoole Loader extension.
Security Features of Swoole Compiler
Swoole Compiler combines several layers of anti-analysis and anti-reverse-engineering protections:
- Binary compilation
The original PHP source is converted into binary instruction data rather than stored as encrypted plaintext. - Advanced obfuscation techniques
Protection mechanisms may include control-flow obfuscation, junk instruction insertion, variable and function renaming, virtual-machine-style execution layers, code flattening, and optimisation techniques such as Sparse Conditional Constant Propagation (SCCP). - Asymmetric cryptography
RSA-based key systems can be used during the protection and verification process, separating signing and validation responsibilities between private and public keys. - Protected loader extension
Decryption logic, licensing checks, and runtime validation are implemented inside a native PHP extension written in C/C++. Because the loader is compiled as a binary shared library, analysing it is substantially more difficult than inspecting ordinary PHP scripts. Additional packers or commercial obfuscators may also be applied to the extension itself. - Hardware or server binding
Protected applications can be locked to a specific environment using machine identifiers such as MAC addresses, CPU IDs, or other hardware fingerprints integrated into the licensing system.
How Decoding Works
Recovering executable logic from protected files generally involves analysing the runtime protection chain step by step. A common approach is to inspect or debug the loader extension while the protected script is being executed, allowing decrypted opcode data to be observed in memory after the loader has processed it.
Once the runtime structures are available, the Zend Engine opcode arrays can be extracted and analysed. From there, the opcode stream may be reconstructed into readable PHP-like source code using a decompiler.
Another common technique is hooking into the PHP Zend Engine itself to intercept opcode generation or execution at runtime, which can expose the decoded instruction stream before execution continues.